While going digital presents companies with numerous benefits, like cost savings and convenience, it also increases the risk of data breaches. Data incidents today are on the rise, with many prominent companies experiencing personal data leaks. In this landscape, securing sensitive data and maintaining user privacy become extremely challenging, yet important tasks.
Multi-factor authentication (MFA) is one excellent way to fend against unauthorised access in the cyber world, offering an additional layer of protection beyond what traditional username and password combinations can provide. From a user’s perspective, implementing MFA can also offer numerous benefits. To ensure the utmost security and a seamless user experience, businesses must adopt a strategic approach. We’ll share some best practices below.
1. Choose the Right Authentication Factors
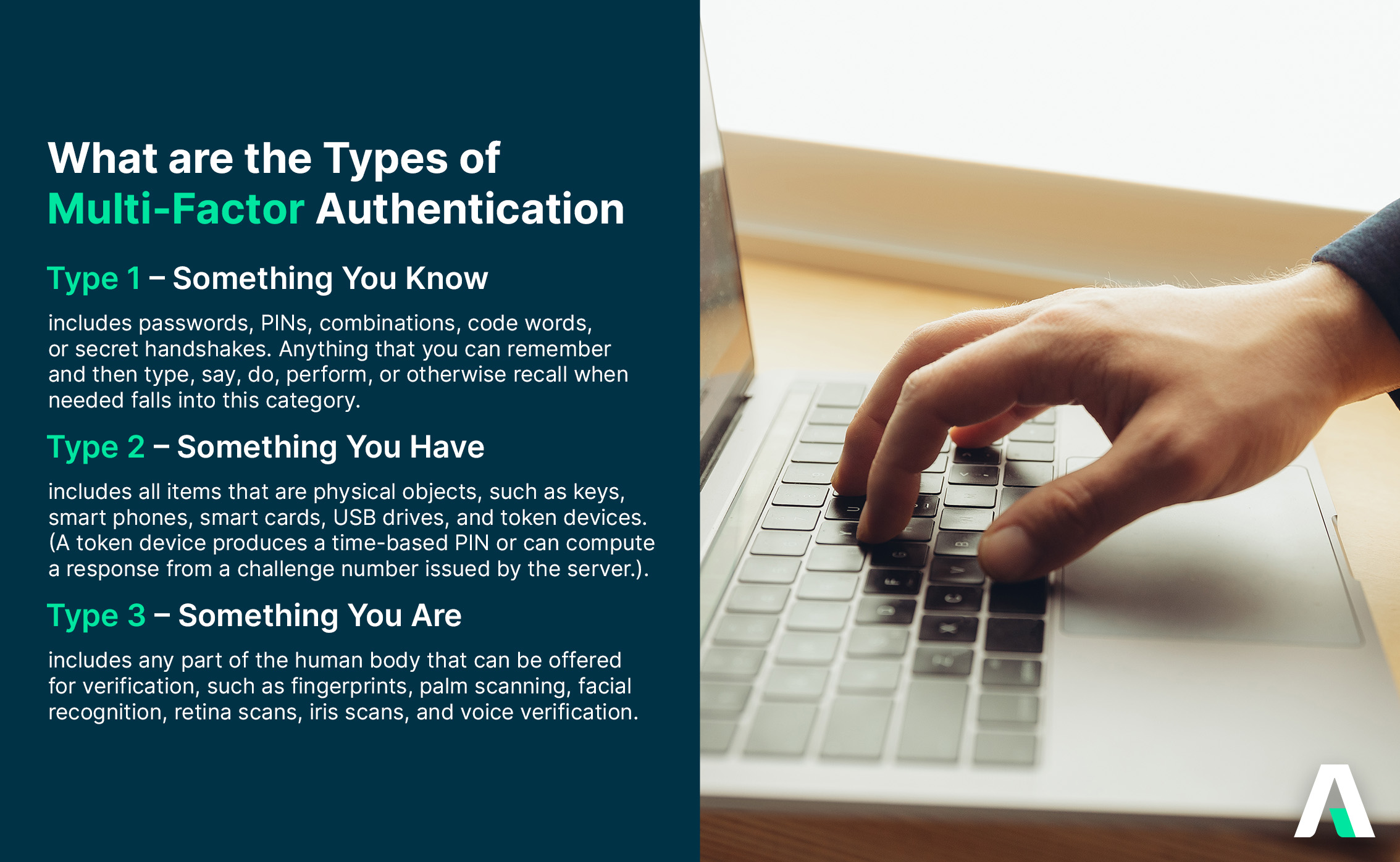
Authentication factor selection based on your company’s security needs and user preferences is the first step organisations should take towards building a robust MFA system. There are numerous ways to verify identities—biometrics, passcodes, tokens or cards—and having a variety of them allows your team to choose what works best for them while ensuring defence.
When deciding the methods of authentication to employ, consider conducting user surveys to help your organisation better understand what your users prefer. This user-centric approach will bring forth a myriad of benefits for both the users and the organisation, including enhanced security, higher adoption rates, and improved user satisfaction.
2. Integrate Adaptive Authentication
Static MFA setups may not be sufficient to combat sophisticated attacks. This is when adaptive authentication strategies come into play. They are able to assess user behaviour and risk factors to determine the appropriate level of authentication and introduce additional verification steps when they sense an increase in risk or any suspicious behaviour.
Adaptive authentication also intelligently adjusts security measures based on real-time factors, such as user location, time of day, and device type. If a user attempts to log in during an unusual time, such as late at night, the system may perceive an increased risk due to a deviation from established patterns (e.g. usual day time access from predictable locations around the premises). It will then trigger a second factor of verification, even if the initial credentials are correct. These features not only enhance security, but also adapt to users to improve the overall experience.
To integrate adaptive authentication and optimise (MFA), follow these key steps.
- Define authentication policies by identifying factors like user location and behaviour for risk assessment.
- Utilise a risk assessment engine to dynamically evaluate login attempts based on these factors.
- Choose appropriate authentication methods corresponding to the risk level.
- Implement a variety of MFA methods, like biometrics or tokens.
- Ensure compliance with relevant regulations, conduct thorough testing, and gather user feedback.
3. Conduct Regular Risk Assessments and Security Audits
- Clearly define the scope of the assessment and determine the assets, processes, and data that require protection.
- Compile a comprehensive list of all assets involved in the MFA system.
- Identify potential threats and vulnerabilities, both internally and externally, as well as emerging cyber threats, that could compromise your MFA system’s security.
- Conduct penetration testing to simulate real-world attacks, uncover potential risks, and assess the system’s resilience.
- Perform vulnerability scans on the MFA system using automated tools to identify and assess known vulnerabilities, misconfigurations, and weak points. This helps you ascertain which areas to improve before they become entry points for unauthorised access.
- Review and update security policies related to MFA and ensure that they align with industry best practices.
- Assess the effectiveness of user training programmes related to MFA. Ensure that users are aware of compliance requirements and understand how to utilise MFA tools properly.
- Review and update the incident response plan for MFA-related incidents.
- Document any findings, recommendations, and actions taken during the assessment.
- Implement continuous monitoring mechanisms to detect and respond to security events in real-time.
Additionally, pay attention to user feedback regarding authentication processes during security audits. Are there common pain points or user complaints? Addressing these issues can lead to a more user-friendly MFA experience.
4. Enable Role-Based Access Control

Role-based access control (RBAC) is another feature to have when implementing MFA. It’s grounded in three core principles—role assignment, role authorisation, and role-based permission assignment—ensuring that only authorised users can access specific system areas based on their responsibilities. For example, only finance personnel can retrieve finance-related information and data. This way of granting permission subjects even legitimate users to heightened authentication when attempting to obtain sensitive information. Apart from enhancing security by reducing attack surfaces and limiting potential damage in the event of a breach, RBAC also improves efficiency in managing user permissions and creates a more organised and scalable access control system.
5. Ensure Compliance with Regulations
The implementation of MFA requires compliance with specific government regulations. When optimising your MFA system, ensure that it not only fortifies security but also meets the necessary legal standards. Different industries and regions have varying compliance requirements. Do find out more about the relevant guidelines your business should be adhering to. For example, financial institutions may need to comply with guidelines set by the Monetary Authority of Singapore (MAS). Non-compliance can result in hefty fines and reputational damage, which can be detrimental to businesses.
6. Consider Scalability and Flexibility
As your business grows, so does your user base. In order for your MFA solution to expand with your organisation, it should contain scalability features that can accommodate increased authentication requests without compromising performance. Choose a solution that can adapt to changing technology trends and user preferences, as maintaining a responsive and efficient MFA system as you grow can be vital for positive user experiences.
Cloud-based MFA solutions are great options to consider. The nature of these systems allows for the effortless integration of new users without compromising performance and enables swift adaptation to changing technology trends. This flexibility contributes to its scalability and can be an indispensable asset for growing organisations.
7. Integrate with Cloud Identity and Access Management (IAM) Systems
One way to increase your MFA system’s flexibility and scalability is to integrate it with cloud IAM systems. This will enable the automatic reflection of modifications, such as profile updates or role changes, in the MFA setup, providing a centralised and efficient approach to managing user identities and access permissions. With the ability to swiftly respond to changes, businesses not only simplify administrative tasks but also reinforce security by reducing the potential for human error in manual adjustments. Users will appreciate the ease of access while your organisation benefits from the added security layers.
8. Single Sign-On (SSO) Integration
MFA can lead to an increase in hassle as teams need to go through more than one step for verification. SSO integration helps to strike a balance between security and convenience by letting users access multiple applications with a single set of credentials. This way, they’ll only have to go through the MFA process once to be able to retrieve various services or data.
For example, SSO streamlines the login process for employees attempting to gain access to enterprise applications. Rather than remembering and entering different sets of credentials for each software or platform, they can use a single set, such as a username and password, to enter multiple applications. This saves time, minimises the chances of password-related issues, and reduces frustration among employees while enhancing security.
In cases where customers are required to access different online services, SSO integration also helps users seamlessly navigate across the platforms by enabling one-time log-ins using a single set of credentials. The result is a more intuitive and efficient online experience, fostering positive interactions and optimising the customer journey.
9. Optimise with Singpass
Singpass, short for Singapore Personal Access, is a government-issued digital identity for citizens and residents of Singapore. It serves as the gateway to access various government services online, providing an additional layer of security through MFA.
Organisations can tap into Singpass API integration to introduce a seamless and secure way to authenticate users accessing online services. It enhances traditional username-password verification methods by presenting two additional authentication factors: biometric verification and a one-time password. This 2FA setup helps to increase protection against unauthorised access while maintaining user convenience.
Learn More: Singpass: Empowering Business Growth Across Businesses in Singapore
Want to find out more about strengthening your MFA setup with Singpass integration?
Adnovum is a Swiss IT company that delivers secure digitalization of business processes. Our core competencies span the development of customised software, IAM consulting, cloud data security, IT consulting services, compliance solutions and cyber security services. Register for a complimentary consultation with our specialists to clarify any questions you may have about your digital transformation journey.